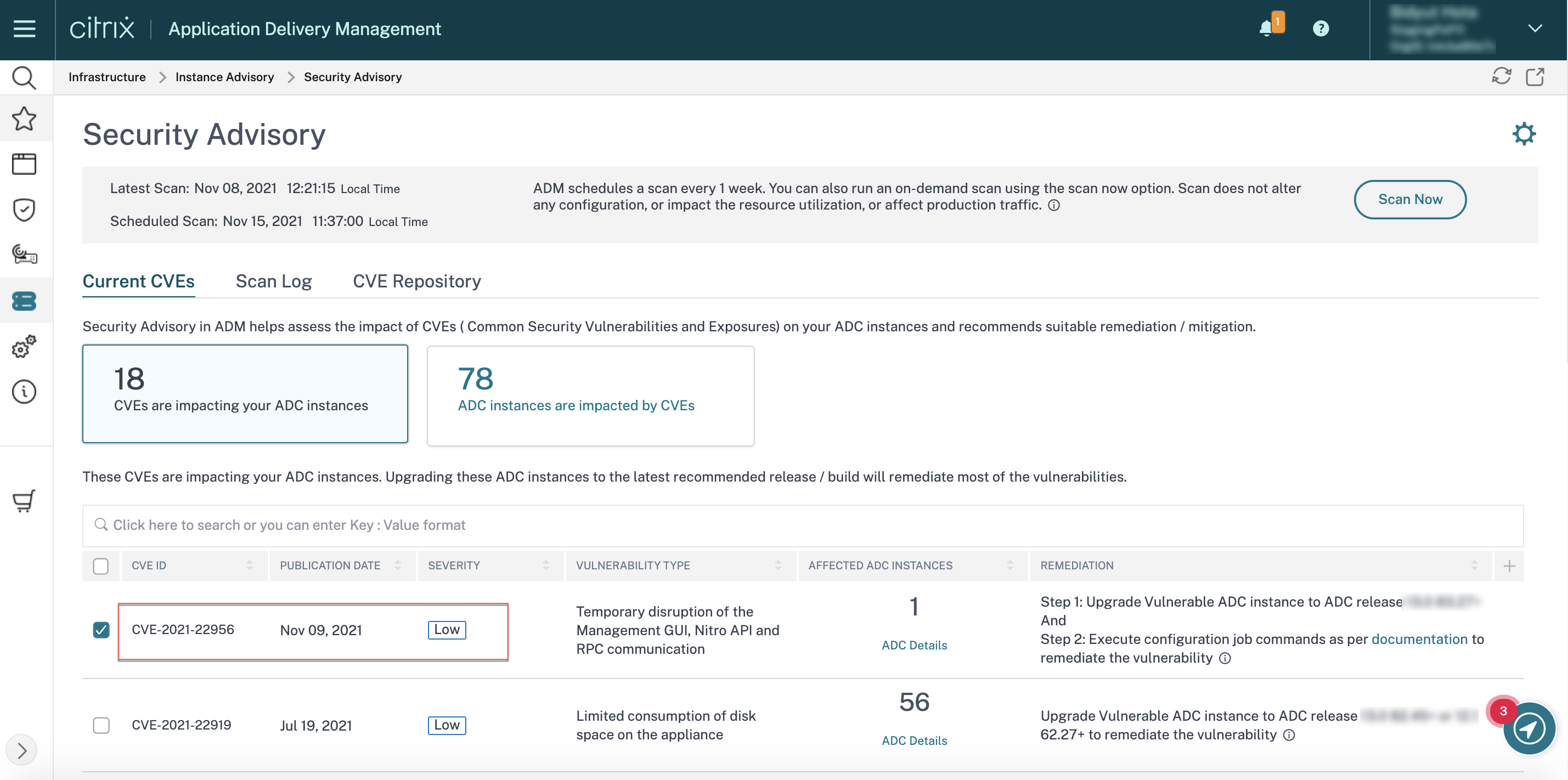
CVE-2019-19781, what you should know and how to fix your Citrix ADC, Access Gateway and SD-WAN WANOP - Poppelgaard.com

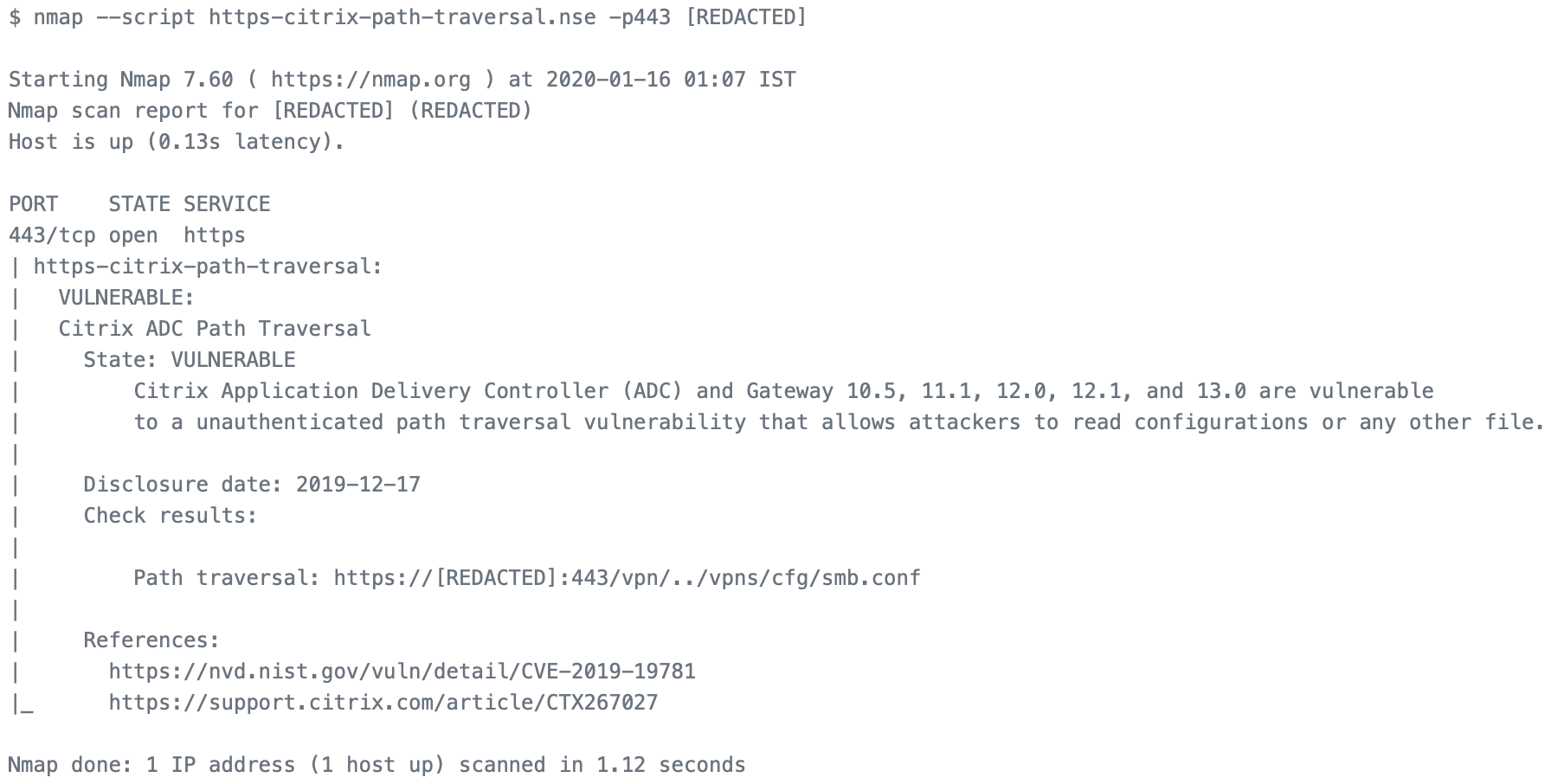
CVE-2019-19781: Critical Vulnerability in Citrix ADC and Gateway Sees Active Exploitation While Patches are Still Not Available - Blog | Tenable®

CVE-2019-19781: Exploit Scripts for Remote Code Execution Vulnerability in Citrix ADC and Gateway Available - Blog | Tenable®
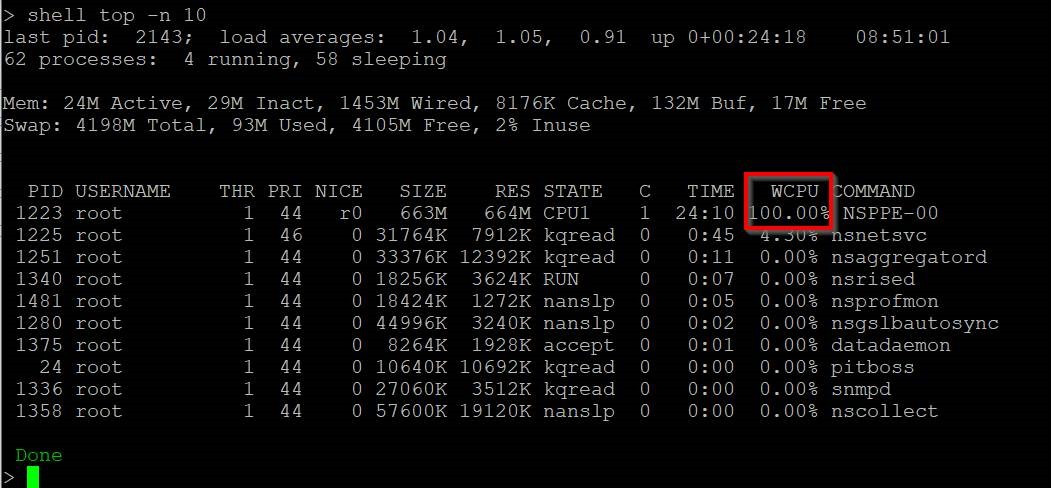
CVE-2019-19781, what you should know and how to fix your Citrix ADC, Access Gateway and SD-WAN WANOP - Poppelgaard.com
GitHub - x1sec/citrixmash_scanner: A fast multi threaded scanner for Citrix ADC (NetScaler) CVE-2019-19781 - Citrixmash / Shitrix

RIFT: Citrix ADC Vulnerabilities CVE-2020-8193, CVE-2020-8195 and CVE-2020-8196 Intelligence – NCC Group Research

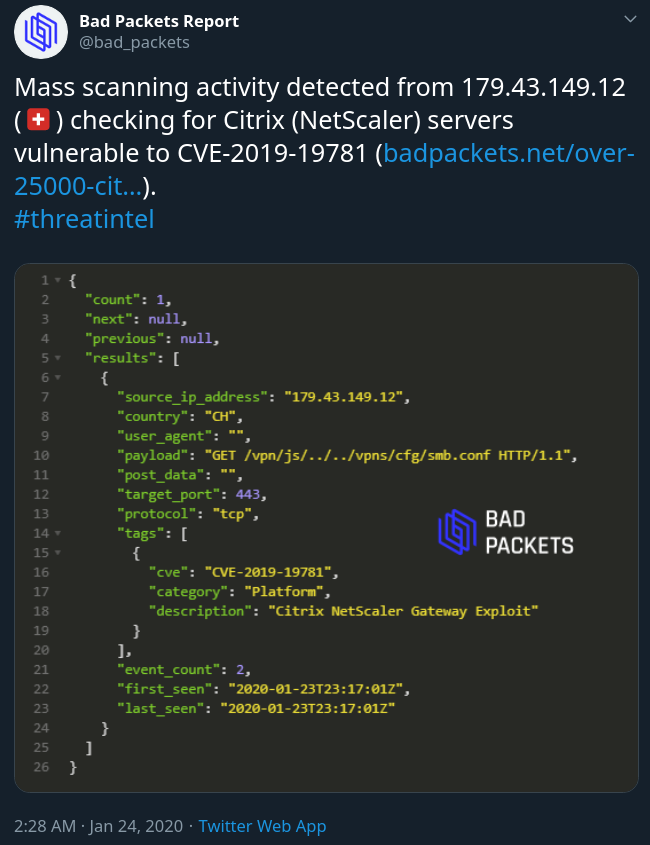
Bad Packets on Twitter: "Mass scanning activity detected from 82.102.16.220 (🇩🇪) checking for Citrix NetScaler Gateway endpoints vulnerable to CVE-2019-19781. Affected organizations are advised to apply the mitigation steps provided by Citrix

How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard

How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard
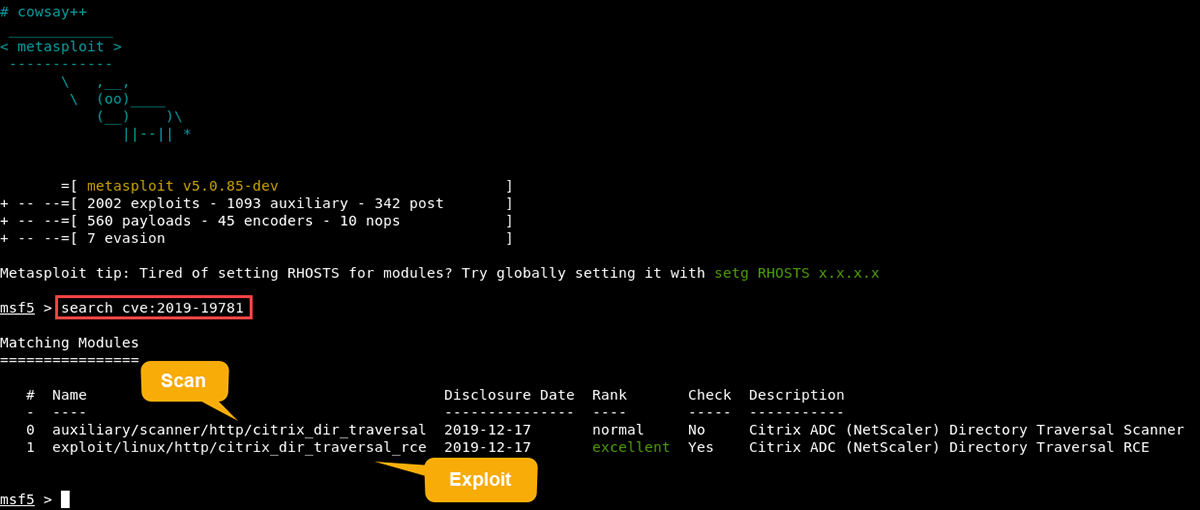
GitHub - mpgn/CVE-2019-19781: CVE-2019-19781 - Remote Code Execution on Citrix ADC Netscaler exploit